Customer connections are evolving. With each driving year, inventions in ease, safety and cost-effectiveness revolve around transactions done online. But as the advantages of on line transactions multiply, therefore do the dangers taken by both Scannable fake ID and consumer.
Hackers, scammers and identification robbers build new ways to use both parties just like easily as they modify to safeguard themselves from attack. It is important in today’s industry for those participating in on line business to take activity to safeguard themselves, their consumers and their opportunities with solid identification affirmation and authorization tools.
When searching for the correct system to safeguard your pursuits, the huge difference between these two components may become obscured, particularly in terms of government regulation compliance. In reality, the recent delay of the Federal Industry Commission’s (FTC) Red Flags Rule implementation date from June 1 to Nov 1 was due to of distress over for whom, and as to the capacity, compliance procedures should be implemented. It’s very important to all business homeowners to know and agree to the level of identification security that’s suited to their needs.
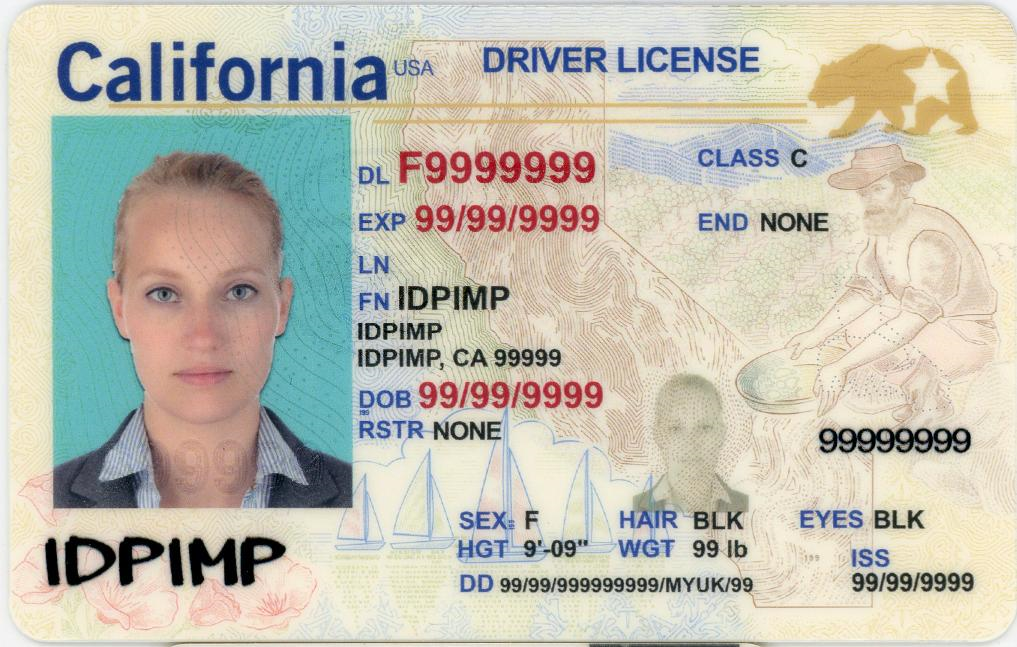
When you have ever been requested to show a driver’s licence, enter a Social Protection number, or present other qualifying particular data before a exchange could proceed, you have experienced identification verification. In other words, identification affirmation is just wondering a consumer to provide an application of identification out of his / her wallet to demonstrate who they are.
While identification affirmation alone is necessary for many businesses and is just a supplementary later of safety for the others, it is not foolproof. From fake IDs to intricately designed scams, people who could use businesses are rapid to function around identification verification. And these workarounds mean that businesses, consumers and confidential data might be at serious risk. That’s where authorization comes in.
When verifying a consumer’s identification in person, there might be nonverbal cues or simple inconsistencies that attentive a small business manager to probable identification fraud. But, these cues are hidden for on line transactions. In the world of complete get automation, if the consumer may fool the safety project, the consumer may set your company at risk.
Identification authorization not just involves consumers to supply qualifying identification data, in addition, it involves the individual to supply data that’s not easily stolen or guessed. They are sometimes named “out-of-wallet” issues and may question anything from the titles of nearest and dearest, to the quantity and volume of a past loan payment. Out-of-wallet issues relate to data only the true individual could know.
Implementing both identification affirmation and authorization into your method protects your company from identification scam and assures compliance with the “Know Your Customer” parts of government safety regulations. But, there is extraordinary value in how these programs are implemented into your exchange process.
In other words, if affirmation and identification procedures take too long, are too boring or too scrutinizing, the client may possibly sense uncomfortable and take his / her business elsewhere. Therefore, it’s important to apply affirmation and authorization procedures which are thorough and precise while still respecting the solitude of the consumer and maintaining exchange convenience.